Record Year for HIPAA Enforcement
In the current environment of regulation reduction, it is notable that the Department of Health and Human Services (HHS) received a record $28.6 million dollars in publicized settlements and judgments for HIPAA violations in 2018. These numbers surpass previous years with the closest year on record being 2016 in which HHS collected $23.5 million dollars. These numbers reflect that HIPAA enforcement actions are on the rise.
There are several factors that are leading to this increase in fines:
- A lack of understanding about what encompasses an adequate HIPAA Risk Assessment;
- Failure to attain Business Associate Agreements when applicable;
- Failure to comply with physical, technical and administrative safeguards to secure protected health information (PHI); and
- Failure to implement encryption solutions or alternative adequate measures.
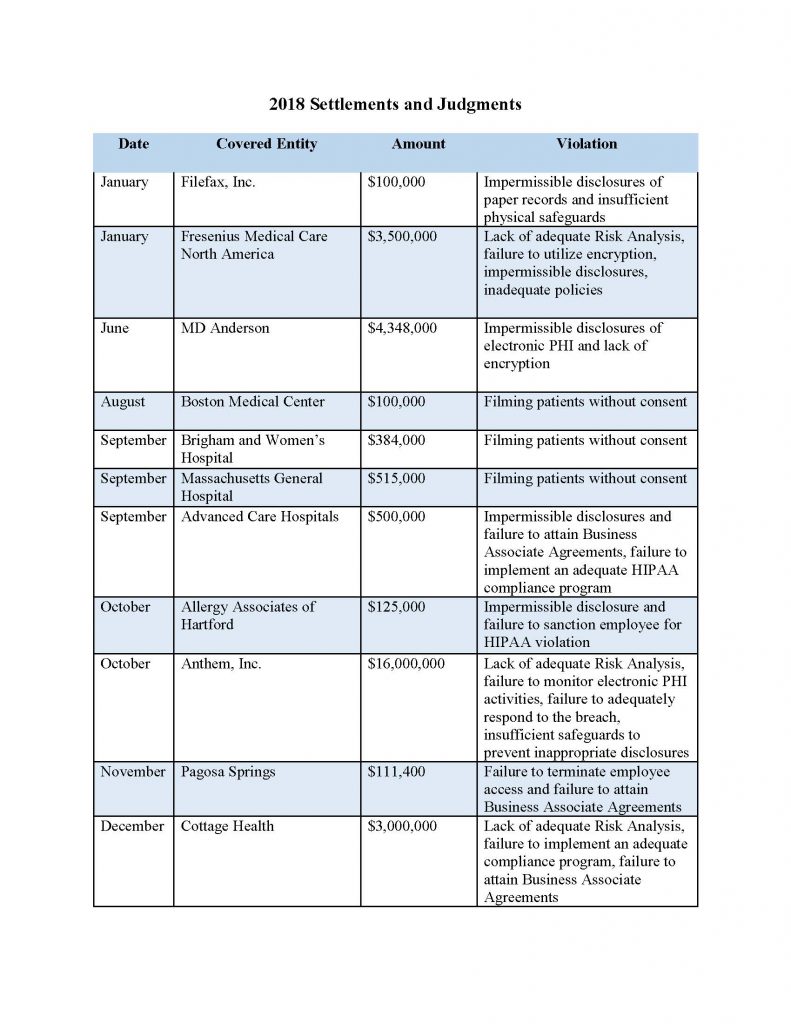
It is important to note that this record-setting total does not encompass all of the enforcement action taken by HHS against covered entities in 2018. These numbers simply represent larger, more notable settlements and judgments. In fact, HHS took corrective action against countless health care providers, health plans and business associates last year and it does not appear that these numbers will decrease in 2019. As of February 22, 2019, HHS has officially begun investigating over 50 entities for large scale breaches. For more information on these investigations of breaches of 500 individuals or more, visit the Wall of Shame on the HHS website. Pursuant to the HITECH Act of 2009, the Secretary of HHS is required to post information about entities who breach the PHI of 500 people or more to demonstrate transparency to health care consumers.
Health care providers can take action to reduce their risk by doing the following:
- Performing annual Risk Assessments;
- Identifying Business Associates and entering into adequate Business Associate Agreements;
- Creating and updating HIPAA policies and procedures;
- Ensuring that employees and staff members receive up-to-date training; and
- Proactive monitoring of electronic systems containing PHI.
This uptick in penalties illustrates that HHS is serious about their mandate to protect the privacy and security of PHI. Their record demonstrates that they can be successful at attaining multi-million dollar settlements with health care entities and health plans that don’t comply with HIPAA regulations. This is a good time for health care providers and HIPAA Business Associates to review their compliance programs to ensure that they are meeting the requirements. In HIPAA compliance, the lack of a specific strategy to secure PHI is an actionable failure that could result in a large fine and a loss of goodwill with the entity’s customers, its patients. If you are unsure about whether your HIPAA compliance program is adequate or if you know that it is time to update your policies, procedures and training, consult a health care compliance expert.
Article contributed by Samarria Dunson, J.D., CHC, CHPC, attorney/principal of The Dunson Group, LLC, a health care compliance consulting and law firm in Montgomery, Ala. Attorney Dunson is also Of Counsel with the law firm of Balch & Bingham, LLP. The Dunson Group, LLC, is an official partner with the Medical Association.
Posted in: HIPAA
Leave a Comment (0) →